The age of robots and artificial intelligence is in its early stages – robots are here to stay for a long time and generations to come.
For decades, robots have played a significant role in sci-fi movies and our imaginations in tandem.
Today, some household appliances such as automated vacuums are robotic. Such popular robotic appliances coupled with IoT functionality are very promising.
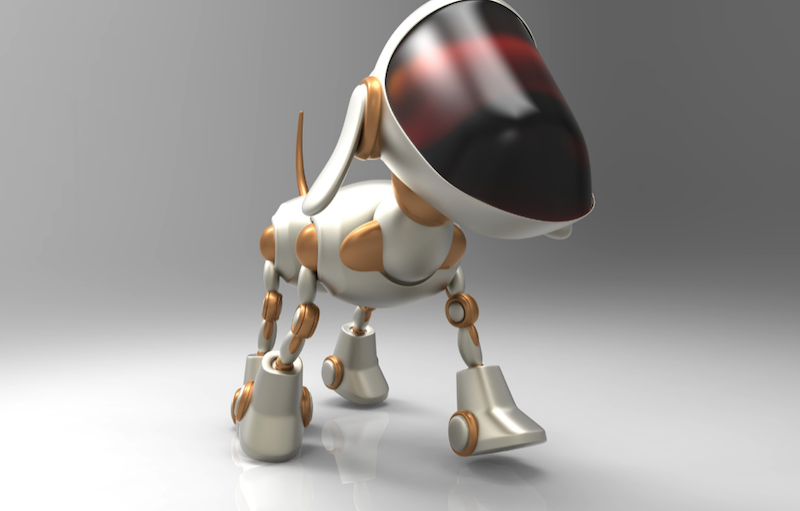
The innovations keep getting more exciting. Robotic toys such as animals are flooding ecommerce platforms and also have potential innovative integrations with IoT, AR, VR and much more.
We may also forget about cyber security matters with all the excitement around robots and their vast far-reaching possibilities and applications.
With the term bot closely linked to the term botnet, many may wonder what is a botnet cyberattack, and how it relates to new potential robot-related cyber security threats.
Many if not all of the technologies related to robotics can spark a new frontier in cyber security. Technologies such as AI (artificial intelligence), ML (machine learning), and advanced automation can fuel a new chapter in the fascinating book of cyber threats.
Some Sound Cybersecurity Advice
Many robotics enthusiasts who are revved to buy the coolest robotic product or are super busy with some robotics-related tech toys, may forget the importance of cyber security on all their endpoint devices such as laptops, desktops, tablets.
Those devices are likely to connect if not already to robotics-related products. These products could exploit and be a gateway to cyberattacking your devices.
The first prudent step is to ensure that you have a comprehensive anti malware anti virus cyber security solution in place across all your endpoint devices.
The solution should be from a reputable and experienced player in the cyber security space with a proven track record.
If you still do not have this level of protection, the next wise step is to download a free trial and evaluate the product and its respective core characteristics.
Characteristics such as UI (user interface) and UX (user experience), online help for the product and other value-added options such as a VPN client and browser level protection should be considered when during the evaluation period.
Once you feel confident with the product, the next step is to purchase the full version to ensure uninterrupted protection across all your devices.
Robots: Potentially in the Hacker’s Toolbox
Robots can integrate into simple and more intricate large scale cyber-attacks in many ways. A hacker can plant malware in a robot pet and turn the pet into a cyber proxy to gain access to devices such as smartphones, tablets, and laptops.
Robot pets can also have listening capabilities to spy on people and gain information to plan a social engineering and other types of simple to elaborate cyberattacks.
A robot pet can be used for corporate espionage, for WFH – work from home and from the office in the case an employee decides to bring their robot pet to work.
The robot pet can collect confidential audio and even video footage of employees’ screens, record it and even send it live in real-time to help a cybercriminal organization create a strong blueprint for a more elaborate attack and even for competitive intelligence which could be sold for large monetary amounts.
Main image: Robot pet dog. Credit Julos via Canva.