By Sjoerd van der Zwaan, chief product officer, Solid Sands
The new EU Regulation 2023/1230 is set to enter force on 20 January 2027, replacing the long-standing Machinery Directive 2006/42/EC.
The implications for machinery manufacturers are profound because the regulation extends the scope of machine safety to include software-driven, autonomous, and AI-enabled systems.
As a result, the need to qualify machine software and its toolchain as part of a continuous, lifecycle-based process comes into sharp regulatory focus.
EU Regulation 2023/1230 extends mandatory safety requirements to digital machine components that were previously addressed only indirectly. Embedded software and AI functionality for industrial robots and cobots (collaborative robots), and autonomous mobile machinery now fall clearly within the regulation’s scope.
For machine builders, it signals a fundamental shift. Software is no longer an implicit contributor to safety; it is formally recognized as an explicit safety component, with direct impact on qualification processes and ongoing compliance.
A new regulatory era
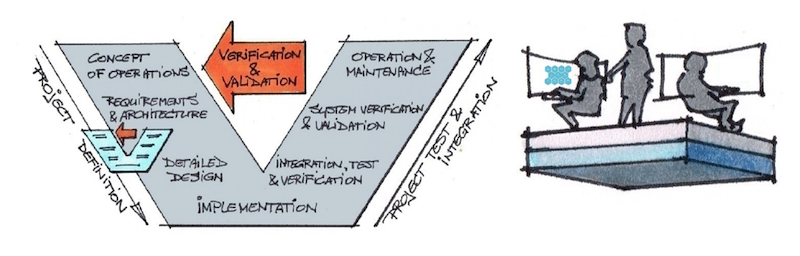
When launching a machine into the commercial marketplace, the manufacturer is responsible for ensuring that its design and build meet safety requirements.
The company must undertake appropriate risk assessments and qualification activities, with high-risk machinery subject to third-party review.
The regulation now makes clear that software-defined safety elements require dedicated compliance scrutiny, reinforcing the need to qualify not only the application software but also the software toolchain used to create it.
Regulation 2023/1230 is closely aligned with the EU’s AI Act and Cyber Resilience Act, forming part of a broader shift toward a horizontal, lifecycle-based regulatory approach focused on sustained compliance.
Together, these frameworks place software and its toolchain at the center of machine safety and compliance. Qualification is no longer a one-time certification milestone; it must be demonstrated and maintained throughout the operational life of the machine.
From static compliance to continuous assurance
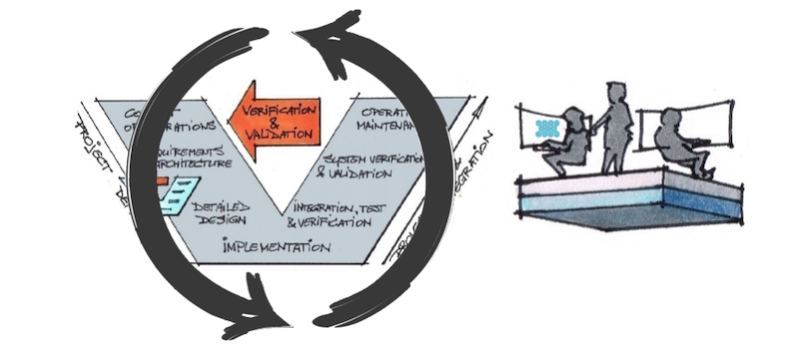
Historically, compliance followed a predictable model: manufacturers qualified their software toolchain once, froze it, certified the product, and avoided changes wherever possible. This approach is increasingly incompatible with modern machinery.
Cybersecurity threats require ongoing patches and updates, and compilers and standard libraries change through bug fixes, performance improvements, and language evolution. Locking these elements down indefinitely conflicts with regulatory expectations that emphasize sustained safety assurance.
In parallel with the AI Act and Cyber Resilience Act, Regulation 2023/1230 reflects this reality. Software is treated as a dynamic element of the safety case; cybersecurity is elevated to a safety objective; and autonomous systems interacting with human operators are now subject to more stringent conformity procedures.
Evidence for continuous assurance
Under this new regulatory environment, authorities expect evidence that the entire software development process is controlled, auditable, and trustworthy.
Compliance now depends on demonstrating how safety is maintained as systems evolve. Rather than freezing toolchains, manufacturers must implement assurance practices that scale with change, supported by continuous verification.
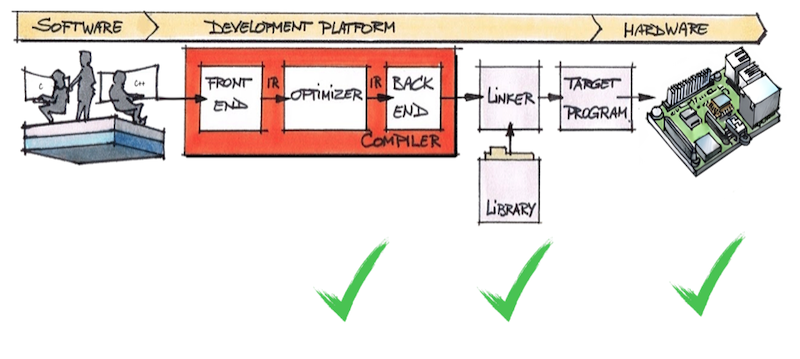
This shift elevates the importance of software toolchain qualification. Compilers and libraries directly influence functional correctness, determinism, and traceability in safety-related control systems.
Optimization mechanisms, while essential for performance and real-time constraints, may introduce subtle risks – for example by altering numerical behaviour or execution paths in ways not visible at application level. Library defects can also propagate through issues such as inconsistent data handling across formats.
The distinction between assuming a software tool works and proving that it works becomes critical. Under the regulation, software is a traceable and assessable part of the machinery safety case, requiring demonstrable qualification.
Evidence must extend from system-level integration testing down to the application software, libraries, and compiler. Effective assurance therefore relies on structured, repeatable testing of the toolchain against defined specifications.
Managing toolchain assurance
Toolchain qualification that delivers confidence across domains such as automotive and industrial is grounded in three real-life use cases: the continuous qualification of compiler and standard library toolchains to maintain regulatory compliance over time; toolchain-centered quality assurance, to reduce latent software risk and anticipate as early as possible eventual later stage certification findings; and the continuous integration (CI) of qualified tool chains.
CI environments enforce the use of qualified toolchains and capture the evidence generated. Automated testing triggered by toolchain updates, configuration changes, or scheduled regression cycles creates traceability between software builds and qualification data.
This evidence can support the maintenance of an existing safety case and identify any deviations that require further analysis.
Closing the gaps
Despite the lengthy and well-publicized transition period of EU Regulation 2023/1230, some machinery manufacturers continue to underestimate the scale of change required before 20 January 2027.
Although their experience with the Machinery Directive will provide a good foundation, the explicit inclusion of software, AI, and cybersecurity brings unfamiliar regulatory expectations.
However, getting it right will deliver benefits that extend far beyond legal obligations. For instance, continuous toolchain qualification reduces latent risk, strengthens engineering confidence, and supports the safe deployment of autonomous and intelligent machinery.
This is because it exposes both strengths and limitations, allowing engineers to design systems that avoid known weaknesses or address them proactively.
Identifying toolchain issues early provides options: adapting code, engaging with tool suppliers, or selecting alternative versions. It also avoids the discovery of issues late in the compliance process, negating any potential forcostly redesign and recertification efforts.
In short, continuous toolchain qualification can become a competitive advantage rather than just a regulatory tick-box exercise.
Time to act
The new EU Regulation 2023/1230, together with the AI Act and Cyber Resilience Act, signals the end of the traditional freeze-assess-qualify model. In its place emerges a lifecycle-based approach built on continuous qualification, continuous quality assurance, and automated evidence generation.
For machine builders, adapting to this model is not optional. It is the legal foundation for placing safe, compliant, and future-ready machinery on the European market.
To begin the transition, machinery manufacturers should adopt a three-step strategy. First, put the toolchain front and center of projects to avoid hidden risks, the potential for which only increases when deploying a complex ecosystem of AI and cybersecurity.
Machine builders need confidence in their toolchains to allow maximum focus on the development of application software and the integration testing thereof.
Second, start migrating to this new strategy as soon as possible as it supports the early detection of problems and their easier resolution. It could even avoid latent issues that only manifest after production commences. Undetected, these issues can potentially lead to risks of actual physical harm, costly recalls, and damage to brand reputation.
Lastly, keep the lifecycle approach in mind: continuous quality assurance and continuous qualification – automated within CI pipelines.
Solid Sands can help machine manufacturers comply with the EU Regulation 2023/1230 through the company’s proven test, validation and qualification suites: SuperTest for C and C++ compilers; and SuperGuard for C and C++ libraries. Both suites are available as a cost-effective, subscription-based payment model.

About the author: Sjoerd van der Zwaan is a technology leader specializing in artificial intelligence, computer vision, and robotics, with extensive experience building and scaling engineering teams and delivering customer-focused solutions. He is chief product officer at Solid Sands, and his work focuses on shaping product strategies that bridge advanced technical capabilities with real-world customer needs.