Understanding how internet traffic is managed behind the scenes often feels like looking inside a glass wall – you know something is there, but you don’t always notice it. That is exactly where the concept of a transparent proxy fits.
It operates quietly, without asking users for permission or configuration, yet it plays a powerful role in how data flows across networks. So, what is a transparent proxy, and why does it matter so much in today’s digital infrastructure?
The Core Idea Behind a Transparent Proxy
A transparent proxy is an intermediary server that sits between a user and the destination website, routing traffic without requiring any action from the user.
Unlike other proxy types, it does not need manual setup in a browser or application. From the user’s perspective, everything feels direct and natural, as if no middle layer exists at all.
Think of it like an automatic toll road sensor. You drive at normal speed, no stopping, no tickets, no gates – yet your car is still identified, monitored, and processed by the system.
A transparent proxy works the same way. Requests pass through it automatically, allowing network administrators to observe, optimize, or manage traffic without interrupting the user experience.
How Transparent Proxies Operate Behind the Scenes
At a technical level, a transparent proxy intercepts traffic at the network layer. This usually happens through router or firewall rules that redirect traffic to the proxy server. Because of this design, the user’s device does not even realize a proxy is involved.
The proxy then forwards the request to the destination server and relays the response back to the user. Since no client-side configuration is required, transparent proxies are commonly used in environments where administrators need broad control – such as corporate networks, schools, hotels, and public Wi-Fi systems. The goal is efficiency and oversight, not user interaction.
Common Use Cases for Transparent Proxies
Transparent proxies are not about complexity; they are about scale and control. They shine in environments where managing large volumes of traffic is more important than individual customization.
Here are some of the most common scenarios where they are applied:
- Traffic monitoring to understand usage patterns and network load
- Content filtering in corporate or educational networks
- Caching frequently accessed resources to reduce bandwidth usage
- Policy enforcement for acceptable use and compliance
- Performance optimization by reducing latency on repeated requests
Each of these use cases benefits from the same core advantage: the proxy works invisibly, without user involvement.
Transparent Proxy vs Other Proxy Types
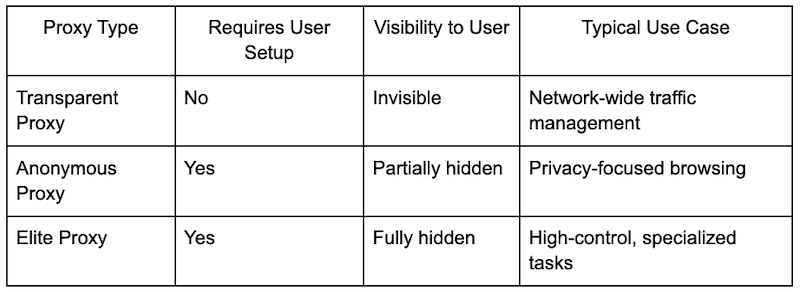
To better understand where transparent proxies stand, it helps to compare them with other proxy models. The key difference lies in visibility and configuration.
This comparison highlights why transparent proxies are favored by administrators rather than end users. They are designed for control at the infrastructure level, not for individual customization.
Advantages and Limitations You Should Know
Every technology is a trade-off, and transparent proxies are no exception. Their biggest strength – being invisible – is also their biggest limitation.
On the positive side, they are easy to deploy at scale, require no user training, and allow centralized traffic control. They are excellent tools for organizations that need oversight without friction.
On the downside, because users are aware of their presence, transparent proxies are not suited for tasks that require user-level control or flexibility.
It’s a bit like automatic climate control in a large office building. It keeps the environment stable and efficient, but you don’t get to fine-tune the temperature at your desk.
Where Transparent Proxies Fit in Modern Infrastructure
In modern network architecture, transparent proxies are often combined with other proxy solutions to create layered systems. A company might use transparent proxies for baseline traffic handling while relying on configurable proxy services for specialized tasks and external operations.
This is where professional proxy providers, such as Proxys.io, come into play – offering structured, reliable solutions that complement internal network tools rather than replacing them. The transparent proxy handles the “silent work,” while other proxy types manage more visible, task-specific workflows.
Why Transparent Proxies Still Matter Today
With cloud services, distributed teams, and massive data flows becoming the norm, the need for quiet, efficient traffic management has not disappeared.
If anything, it has grown stronger. Transparent proxies remain relevant because they solve a simple but critical problem: how to manage and optimize network traffic without slowing people down or forcing configuration on every device.
In many ways, they are the unsung heroes of network infrastructure. You don’t notice them when they work well – but when they’re gone, the system quickly feels less organized, less efficient, and harder to control.
Final Thoughts on Transparent Proxies
So, what is a transparent proxy? It is a behind-the-scenes architect of network flow, shaping how data moves without ever stepping into the spotlight. For organizations that value control, efficiency, and simplicity, transparent proxies are not just useful – they are essential.
Understanding how they work gives you a clearer view of the invisible systems that keep modern networks running smoothly. And once you see that glass wall, you start to appreciate just how much is happening on the other side.