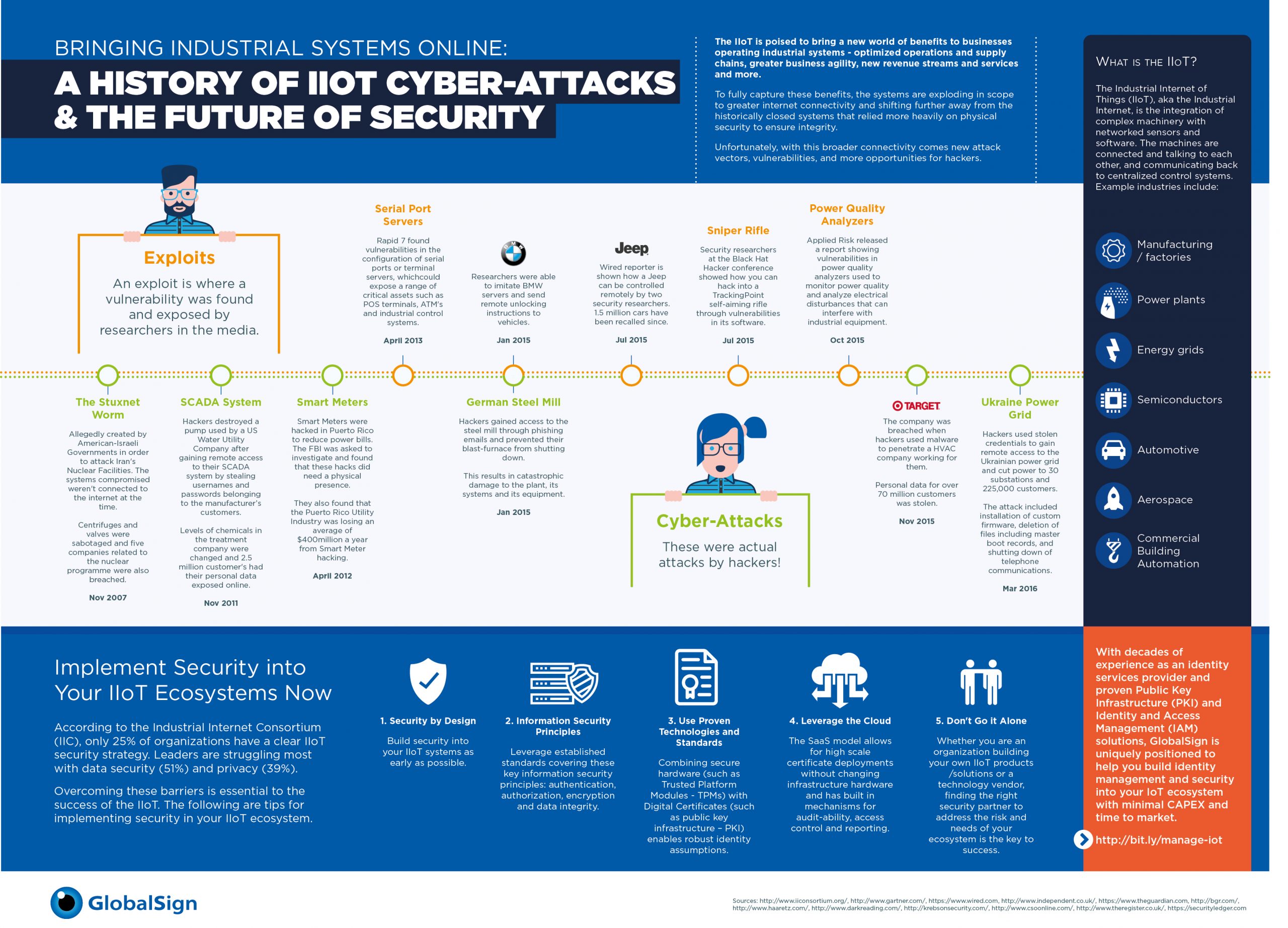
GlobalSign has produced an infographic which provides some insight into the history of cyber attacks against the industrial internet of things
The Industrial Internet of Things, or Industry 4.0, is improving operational efficiencies for global industrial systems on a scale never seen before.
The IIoT holds great potential for improved communications, productivity, quality control, supply chain efficiencies and overall business operations. With this broader connectivity, comes new attack vectors, vulnerabilities and opportunities for hackers.
When you start to consider the various IIoT cyber-attacks and exploits in the last decade, the damages are startling.
GlobalSign, a provider of security solutions for the IoT, has created an infographic (above) with real-life security incidents as a way to show the magnitude of threats.
Of course many of these are exploits where a vulnerability was found and exposed by researchers and gained media attention. For example, the well-known Miller/Valasek Jeep hack chronicled by Wired Magazine; and just recently the cybersecurity research duo was at it again, demonstrating the full consequences of a digital attack, had a security patch not been updated.
The green spots on the infographic’s timeline represent actual attacks carried out by malicious hackers, like the Target data breach, or most recently the Ukraine Power Grid hack that occurred in December, where hackers used stolen credentials to gain remote access to the grid and cut power to over 200,000 customers.
The IIoT encompasses a myriad of industries such as manufacturing, power plants, energy grids, semiconductors, automotive, aerospace and commercial building automation. So whether it is connecting cars, outfitting smart buildings, bringing intelligent cities online or manufacturing in factories of the future, the time to implement security into your IIoT ecosystems is now.
GlobalSign offers the following tips for implementing security:
- Security by Design: Build security into your IIoT systems as early as possible as changes are much easier and more cost effective to make early in the product lifecycle, especially as proper security and privacy features are rarely ever “bolt-on.”
- Information Security Principles: In regards to building IoT/IIoT products, some of the core information security concepts are authentication (authenticating devices to cloud services, between users and devices and from thing to thing), encryption (which allows for private communications) and data integrity (to ensure messages can be trusted and have not been altered in transit).
- Use Proven Technologies and Standards: Combining secure hardware, like Trusted Platform Modules (TPMs) with Public Key Infrastructure (PKI) enables robust identity assumptions.
- Leverage the Cloud: The SaaS model allows for high scale certificate deployments without the cost and set up of on premise hardware.
- Don’t Go It Alone: Finding the right security partner is key to realizing the business benefits of the IIoT.